SQL injection - how to attack an SQL vulnerability with complete control

SQL Injection: The Hacker’s Backdoor to Your DataПодробнее

Cybersecurity Shorts: Day 44 - What is SQL Injection ?Подробнее

Master SQL Injection Attacks: Full Control Exploitation | Learn SQL InjectionПодробнее

How Does SQL Injection Work?What is SQL Injection?Подробнее

How SQL Injection Works #linux #sqlinjection #cybersecurity #ethicalhacking #infosecПодробнее
4 Ways to Hack a Website!Подробнее

code injection attack | Control any websites in Minutes!Подробнее

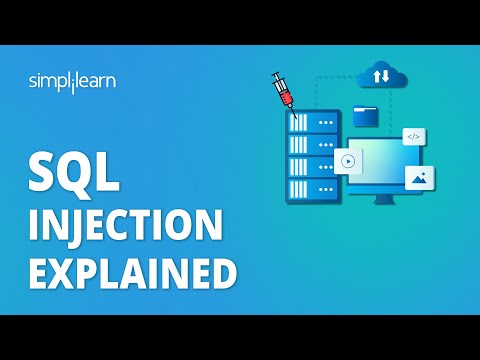
SQL Injection Explained | SQL Injection Attack in Cyber Security | Cybersecurity | SimplilearnПодробнее
Hacking with SQL Injection, Exploiting several vulnerabilities and gaining control of a server!Подробнее

SQL Injection For BeginnersПодробнее

13.7. Reading & Writing Files On The Server Using SQL InjectionsПодробнее

13.9. Discovering SQL Injections & Extracting Data Using SQLmapПодробнее

13.2. Discovering Complex SQL Injection VulnerabilitiesПодробнее

13.3. Exploiting an advanced SQL Injection Vulnerability to Extract PasswordsПодробнее

11.2. Bypassing Logins Using SQL Injection VulnerabilityПодробнее

11.3. Bypassing More Secure Logins Using SQL InjectionsПодробнее

advanced-sql-injection-to-operating-system Full ControlПодробнее
