EchoCTF - CTF Beginners Network - Idiotr - Web Hacking - IDOR Vulnerability

Exploiting IDOR Vulnerabilities | APISECCON CTF 2024 | Part 1Подробнее

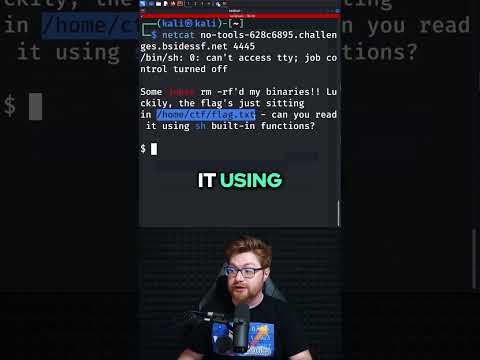
No Tools in a CTFПодробнее
How hackers trick you online (Social Engineering Explained) - 0xcodeПодробнее

How to Exploit IDOR VulnerabilitiesПодробнее

echoCTF.RED Writeup for CVE-2019-14813Подробнее

Poc of IDOR worth $1250🤑 | Bug Bounty | HackeroneПодробнее

Easily Exploit IDOR Vulnerability | TryHackMe Neighbour | Ethical HackingПодробнее

Как хакеры ломают приложения? | CTF | Hacking | Reverse EngineeringПодробнее

$1500 Bounty || Easy to find IDOR | POC | Bug Bounty | Spreaker.comПодробнее

idor pocПодробнее

Web Ethical Hacking Tools - ffuf with IDORПодробнее

idor vulnerabilityПодробнее

IDORПодробнее
